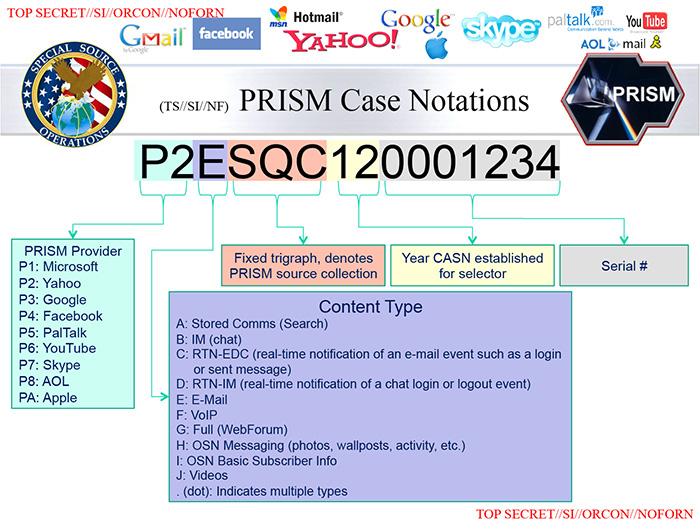
New details have been revealed about the NSA PRISM program, which allows the United States government to snoop on internet traffic from major tech companies like Google, Facebook, Yahoo! and Apple. The Washington Post has posted the top secret slides from the NSA, which shows exactly how PRISM’s real-time data tracking works.
One slide seemingly confirms Edward Snowden’s claims that the NSA has access to real-time data from email and instant messaging, which flags a targeted person as soon as he or she is online.

There’s also a slide showing the amount of collateral data collecting that the NSA has while pursing a target. Dated April 5th, 2013, the side shows that 117,675 simultaneous records we being recorded, though it doesn’t specifically state how many of these were from US users or how many relevant records there were.

One particularly interesting slide shows exactly how the data collection process works. The NSA data analysis is broken up into different tools with secret names such as NUCLEON (voice analysis), PINWALE (video analysis), and MARINA (internet records). While the FBI cross-references its own database with stored records to check that they do not match US citizens, live surveillance doesn’t apply. This means that real-time data collected could potentially lead to the collateral collection of data from innocent US citizens.
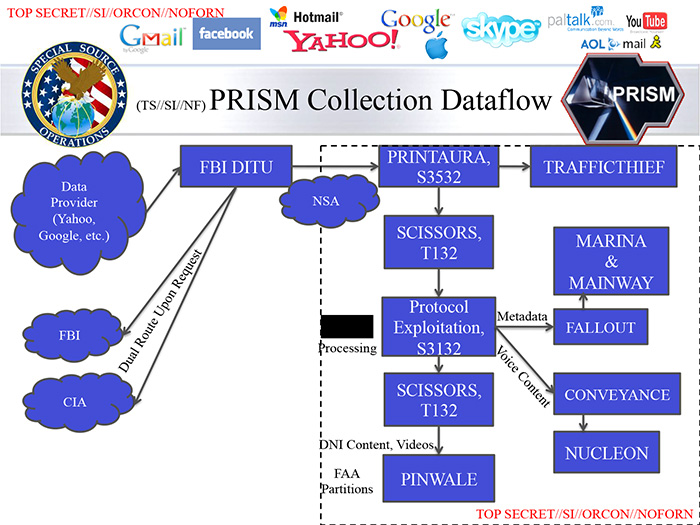
While the leaked sides do show more information about PRISM, there’s still a substantial amount of uncertainty about the program. One looming question that remains is if the NSA has direct and unencumbered access to data from companies like Google, Apple, and Facebook. There’s also no mention of the tactics that actual terrorists can use to mask their identities with things like VPN and data encryption.
[Source: The Washington Post]

