“I’m the Creeper: catch me if you can.” This message, which sounds like it came straight out of a Victorian nursery rhyme, is what was displayed by Creeper, the first virus in history, programmed in 1971. Today, we’ll tell you all about it!
Creeper was created by Bob Thomas, a developer at BBN Technologies, which was on the cutting-edge of the emerging tech industry. Thomas programmed Creeper to test if a program could be created to move between computers. In other words, his idea wasn’t to damage PCs, and in fact, only years later was Creeper considered a virus, since this concept wasn’t applied to computers until the 80s.


Computers in the 70s were somewhat bigger than today’s…
But, did Creeper achieve what it set out to do?
Creeper was spread through ARPANET (one of the first computer networks, used by the U.S. Department of Defense) and copied in the system, where it displayed the message I wrote at the beginning of this article. Once displayed, it started to print a file, but then stopped and switched to another PC, undergoing the same process.
Even though it infected a computer when it first appeared, the effects didn’t last long: by jumping to the next PC, it disappeared from the previous one, and so on.
Today, this might seem like a failure, but in 1971, Bob Thomas’ experiment received lots of attention, since the feat of getting a program to jump between PCs had never been achieved without human intervention. His success was the creation of a program that ran quickly from PC to PC… and was the reason behind creating the first antivirus program!
Reaper: Creeper’s enemy
After Creeper, came Reaper (the perfect tool to cut off a creeper). Created in 1973, this program removed the Creeper “virus” from the system, so it can be considered the first “antivirus program.”
Once again, even though this is more of a modern concept, we can call it an antivirus, since it performs the same functions that an antivirus does today.
What we don’t know for certain is who programmed Reaper. Some say it was Bob Thomas himself, who decided to control his “creature.” Others think that its creator was Ray Tomlinson, a developer who years later would create email.

We owe Ray Tomlinson a lot!
Although these two theories are the most plausible, my personal favorite is another: that Reaper was created by several members of ARPANET as an experiment. This group of experts wanted to see if the system was resilient enough to withstand nuclear war and continue providing a communications network. The fact that it involved a high-level military experiment would justify keeping the creators’ names a closely guarded secret.
The legacy of Creeper and Reaper
Although Creeper didn’t fulfill 100% of its goal and Reaper was a very simple performing antivirus, both mark milestones in computer history.
In 1973, the same year that Reaper was created, the author and screenwriter Michael Crichton was the first to apply the “virus” concept to the tech field. He did this in the movie Westworld, where humanoid robots in an amusement park behave like they shouldn’t. Yes, the recent HBO series is based on this legendary movie.
Yul Brynner, Westworld’s most famous robot
But we have to go to 1974, when Rabbit was created, to talk about PC viruses like this. Rabbit was a program that reproduced non-stop, making copies of itself on a single computer until blocking its system, reducing its performance and eventually wiping it out. Yup, here we see bad intentions starting to emerge.
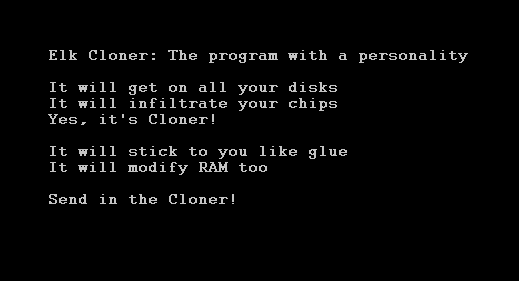
At that time, viruses were called “programs with personality”
A few years later, in 1981, Elk Cloner was created, a virus that affected Apple II (yeah, Apple wasn’t very secure in the past). And in 1986, we said hello to Brain, the first large-scale virus, which affected 20,000 PCs (this time, IBMs), a huge number at the time.
This is when the concept of a computer virus started to be used… if you’re interested, we’ll talk about that history another day.
Sources used for the writing of this article: Techspot, Wikipedia (1, 2, 3), Xataka, Furkangul.

