How To
How to: Control apps accessing Facebook, Twitter and Google

- September 5, 2013
- Updated: July 2, 2025 at 8:12 AM

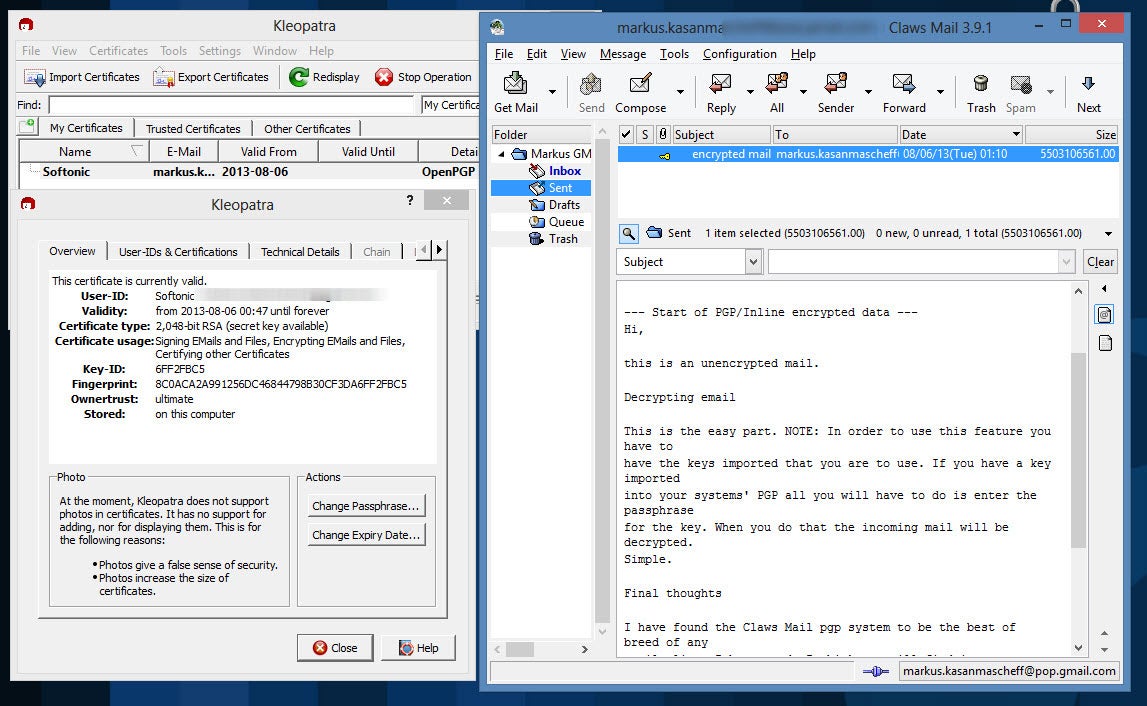
The other day, I received some interesting spam in my inbox. More interesting than most, because it was from a friend. My guess was that my friend had authorized a third party application with a dodgy reputation to have access to his Google account and, consequently, to his Gmail.
My suspicions were founded: as soon as I checked the list of sites for my friend’s authorized applications, I saw one with a strange name. I had a quick search on Google and found that it had a pretty fishy-looking page.
In other words, on the promise of something wonderful, my friend had given a website located in Russia access to his Google account, with all the permissions you’d expect and some you wouldn’t – including the ability to send e-mail on his behalf! I urged him to revoke permissions to the site.
What are unauthorized apps or sites?
Data stored on Google, Facebook and Twitter is invaluable. Some apps and websites access this data through special permissions given by you. But how, and what for?
Third-party apps and sites asking for access to your accounts do so for a variety of reasons. In general, the tasks they perform are very useful, and are meant to enrich the applications you already use. Some examples of apps and sites that need access to your data are:
- Mobile versions of your favorite websites (official or not)
- Websites where you can log in without a password
- Accessories to better manage your email and social networks
- Applications that connect various services such as IFTTT
- Apps that make it possible to back up your data
- Vanity apps: who’s following you, who’s stopped following you or who’s blocked you
It makes sense, right? At the end of the day, you’re always connected to Google or Facebook, so why not use those accounts to enter other pages? Why not allow applications to use your data for your benefit?
The problem is that not all third-party apps or sites are safe, and not all use your data appropriately. If you don’t authorize the app correctly, the consequences can be annoying…or even disastrous.
Why this licensing system?
Since 2007, the network bigwigs began to enable an identification and authorization standard called OAuth (Open Authorization). It’s the standard that’s used when you identify yourself on a page via Google or Facebook.
The reason for OAuth is simple. In the past, in order for these applications to access your data, you had to enter the password for the service, a password that could be captured or stored.
With OAuth, you no longer have to type passwords: Google user authentication is carried out using Google or Facebook. You don’t have to give your password to any third party site, but the site does ask permission from the mother site.
The dark side of authorizations sites
If you’re too quick to authorize apps without thinking about their quality or reliability, you can move into some dark territory filled with predatory apps and sites. Encouraged by the promise of extraordinary things, that’s when we encounter dangerous (or just plain annoying) malware.

Depending on the permissions that you first granted, a malicious app can do varying degrees of damage to your accounts. It can:
- Delete e-mails, updates, contacts
- Send non-requested advertising on your behalf
- Post private photos in public places
- Remove personal information (such as passwords)
These actions do not always have malicious intentions. Sometimes, an authorized site is misconfigured or poorly designed. The damage, however, is the same. But it can be prevented easily: you just need to revoke permissions.
How do I revoke or remove permissions?
All services that grant permissions must allow you to look at those permissions and revoke them at any time. But sometimes it’s not as easy as it seems, either because the necessary option is very well hidden, or because the system for revoking permissions is almost incomprehensible.
Revoking permissions on Facebook

Revoking permission on Twitter
Revoking permissions in Google
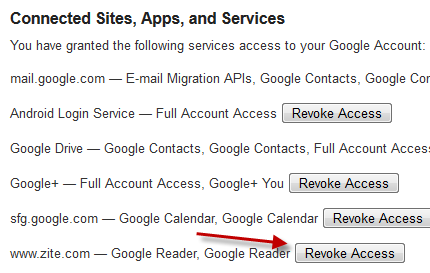
For simplicity, you can use the fantastic page MyPermissions.org and its applications for iPhone and Android, which monitor your services and remind you to clean up the authorizations periodically.
Some tips before we go…
Periodically cleaning up your list of authorized apps is good for your health: it helps you avoid long-term problems when those applications are abandoned or attacked by hackers. But that’s not enough.
You must think before authorizing an app or third party site. What you are authorizing? How reliable is the site? What permissions does it want? If it smells fishy, if it looks too good to be true or looks just a bit dodgy…your mental alarms should begin to sound.
Another helpful tip is to periodically change the passwords you use for core services to ones that are strong but easy for you to remember, using a different one for each service. Using the same password for everything means that if one service fails, they all fail.
Have you had problems with unauthorized apps? Share in the comments below.
Original article written by Fabrizio Ferri-Benedetti, published on Softonic ES.
Latest from Softonic Editorial Team
You may also like
 News
NewsNintendo spent a year breaking melons until they found the perfect sound for 'Donkey Kong Bananza'
Read more
 News
NewsWe already know which legendary group 'Fortnite' will be dedicated to in the coming months. And you won't see it coming!
Read more
 News
NewsColin Farrell's return to 'The Batman 2' will be much smaller than he himself believed
Read more
 News
NewsShould Robert Pattinson join the DC Universe as Batman? Fans of 'Peacemaker' are clear about it
Read more
 News
News'Pokémon Go' announces one of the most important changes in its history, and you'd better hurry up
Read more
 News
NewsSnoop Dogg is afraid to go to the movies because of a kiss in a Pixar movie
Read more