Article
‘Masque Attack’ security flaw lets hackers replace your iOS apps with malicious ones
- November 10, 2014
- Updated: July 2, 2025 at 7:21 AM
Security research firm FireEye published a report today about a new iOS vulnerability that allows attackers to replace your apps with ones that steal your information. FireEye reported the security flaw to Apple on July 26th urging the company to patch it.
This attack, named Masque Attack by FireEye, uses forged bundle identifiers to lure unsuspecting iOS users into installing fake apps. Since iOS doesn’t check for matching certificates for apps with the same bundle identifier, the app is installed without issue.
brightcove.createExperiences();
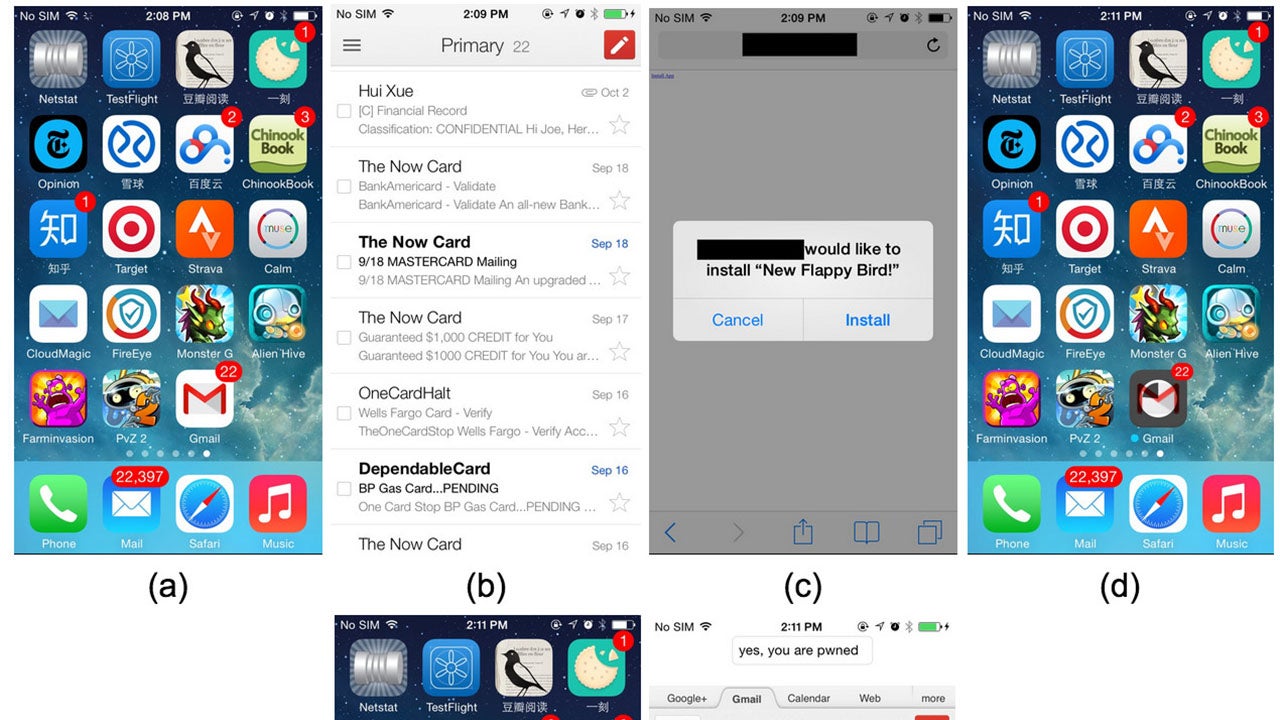
FireEye used a phishing text message to demonstrate how Masque Attack works. If a user taps on the download link in the phishing text, the user will see a pop up asking if they want to install the app. Attackers can name the app anything they want and in this case, FireEye named the fake app “New Flappy Bird.”
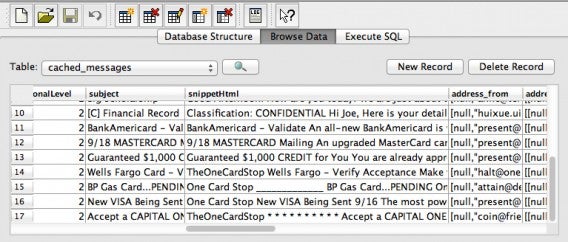
Once the user taps “Install”, the app will replace the legitimate app and the user will be none the wiser. The demonstrated app is a fake version of Gmail that looks just like the official app but secretly sends all of a user’s emails to the hacker.
The scariest thing about Masque Attack is that it works on non-jailbroken iPhones, which means all users running iOS 7.1.1 and up are affected. Even the latest version of iOS 8 isn’t safe. Masque Attack can replace any app downloaded from the App Store but not built-in apps like Safari.
FireEye recommends users avoid installing anything outside of the official App Store. Users should also be aware when an “Install” pop-up is triggered from a web page. Lastly, if you see a warning which reads “Untrusted App Developer”, don’t install the app (duh).
In addition to last week’s WireLurker security vulnerability and now Masque Attack, iOS users are no longer as safe as previously though.
Source: FireEye
Via: 9to5Mac
Related Stories
Computer security should be simple
New iPhone malware spreads when connecting to a Mac
Worldwide governments made 24% more requests for user data in 2014
Windows malware threat Poweliks lives in Windows Registry
Follow me on Twitter: @lewisleong
You may also like
 News
NewsStop Killing Games achieves its first major victory and now it remains to be seen what the European Union will do
Read more
 News
NewsSam Raimi claims that his next movie was going to be a psychological thriller, but that we will probably laugh while watching it
Read more
 News
NewsThe art director of Marathon believes that the game deserves a chance despite everything
Read more
 News
NewsValve's new online shooter will decide which characters to release first through community voting
Read more
 News
NewsThe Dragon Ball Super anime will return after months of hiatus
Read more
 News
NewsIf you've always dreamed of Spider-Man 4, Sam Raimi has bad news
Read more