Article
Security researchers find critical flaws in web-based password managers

- July 14, 2014
- Updated: July 2, 2025 at 7:36 AM

After news of the Heartbleed security flaw broke, I stressed the importance of using password managers to create unique passwords for each site. While password managers help create and store unique passwords, they also offer a single point-of-failure. If someone cracks your password manager, they will have access to all your information across the web.
Late last week, security researchers from the University of California Berkeley released a report of serious vulnerabilities found in web-based password managers. Their research found that five popular web-based password managers could be exploited to reveal user credentials.
LastPass, a massively popular password manager, fell victim to the attack. The most critical bug allowed attackers to steal user passwords out of the password locker without detection.
LastPass’ bookmarklet feature which allowed users to quickly fill in usernames and passwords proved to be insecure. Malicious code implanted on a website could steal credentials from LastPass for other sites.
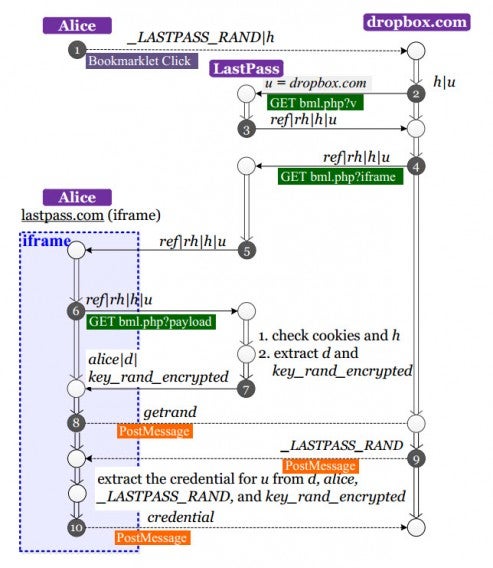
Diagram of the LastPass bookmarklet vulnerability
Other web-based password managers didn’t fare any better. PasswordBox, RoboForm, my1login, and NeedMyPassword were all exploited by similar means. However, every company except NeedMyPassword has patched these vulnerability, making them safe to use again.
“Widespread adoption of insecure password managers could make things worse… After all, a vulnerability in a password manager could allow an attacker to steal all passwords for a user in a single swoop. Given the increasing popular of password managers, the possibility of vulnerable password managers is disconcerting and motivates our work,” writes the UCB security researchers.
Non-web-based password managers like 1Password are unaffected by these vulnerabilities. 1Password developer AgileBits predicted the vulnerability of bookmarklets in 2011, discontinuing the feature.

“In 1Password 4, our browser extension does not store (encrypted or otherwise) user credentials. Nor does our extension handle people’s 1Password Master Passwords. This way, user data and secrets are kept at a further distance from the hostile environment of a third party web page,” said 1Password’s Defender Against the Dark Arts Jeffrey Goldberg. Yes, that’s actually his title.
Does this research mean you should give up on web-based password managers altogether? No, not at all but you should watch to see how each company is reacting. Like I wrote earlier, four out of the five exposed password managers have already patched the exploits.
LastPass recommends users who used the bookmarklet feature before September 2013 to change their master passwords. Users who want to be absolutely sure their data is safe can generate all new passwords for every site they use, but LastPass says they don’t think that’s necessary.
“It’s true that many of the flaws were enormous, but it is also true that vendors (well, all but one) responded appropriately and got those fixed before any damage was done. Both the vendors and the researchers should be commended for how they handled that,” said Goldberg.
Web security is constantly evolving and companies will have to stay diligent to prevent future attacks. It’s extremely difficult to predict and protect against these types of exploits. Developers of password managers will need to work closely with security researchers to maintain the security of their products.
Source: devd.me [PDF] | LastPass
Header image credit: David Goehring [Flickr]
RELATED STORIES
You may also like
 News
NewsGood news! Generation Z is increasingly going to the movie theaters… unlike the rest of the world
Read more
 News
NewsThe new Tekken champion is Japanese and is 92 years old
Read more
 News
NewsOne of the most successful movies of the year premieres on HBO Max
Read more
 News
NewsNaughty Dog is back at it: they are already crunching for their next game
Read more
 News
NewsPedro Almodovar returns with a new movie that is very Christmas-like
Read more
 News
NewsLarian Studios will hold an AMA to clarify their stance on AI early in the year
Read more