Google Chrome is widely regarded as one of the most secure web browsers available today. If you add speed and reliability to Chrome’s high-level security, you can see why it is the most popular browser. There is a chink in Chrome’s armor, however, that has been exploited before and that has again seen hundreds of thousands of Chrome users exposed to malicious code. That weakness is the Google Chrome Web Store.
We reported in October that 30,000 Chrome users had downloaded a fake ad blocker extension that caused their browser to be inundated with ads. On Friday, researchers at security firm ICEBRG uncovered four Chrome extensions that contained malicious code that had already been downloaded 500,000 times from the Chrome Web Store.

The extensions in questions are the HHTP Request Header, Nyoogle, Stickies, and Lite Bookmarks. The researchers discovered that there had been a spike in outbound traffic from one of ICEBRG’s customers and their investigations led them to the extensions mentioned. Each infected the victim’s PC with code that forced the PC to “click” certain advertisements that would generate revenue for the people behind it. According to ICEBRG a similar bot in 2013 generated $6,000,000 a month.
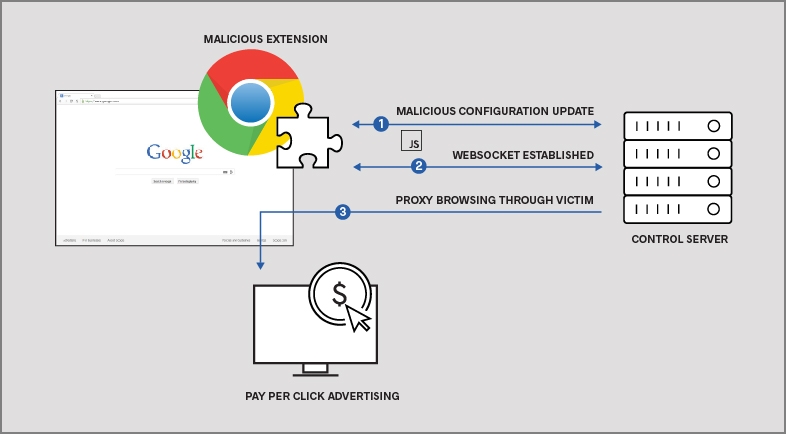
Google removed the malicious extensions from the Chrome Web Store as soon as ICEBRG privately notified it of their presence. In ICEBRG’s report on their findings, however, they pointed out that this type of attack will continue to be attractive to cyber-criminals due to the high payoffs that they offer. They added:
“…without upstream review or control over this technique, malicious Chrome extensions will continue to pose a risk to enterprise networks.”
The ball is definitely in Google’s court on this one. If they want to stamp out this type of scam, they’re going to have to assess their review process for Chrome add-ons. In the meantime, take care when you’re downloading anything from the Chrome Web Store.
Follow me on Twitter: @PatrickDevaney_
Via: ICEBRG and arstechnica


