News
Understanding the Growing Threat of Cybercrime in 2023
Make sure you understand how much cybercrime is evolving and how you can use Norton to defend against it!

- September 20, 2023
- Updated: March 7, 2024 at 2:30 PM

We’ve come a long way since computer viruses first appeared in 1971. Back then, viruses were simply self-replicating software, emulating their physical counterparts. The first one, Creeper, was a “white hat” sort of hacking attempt, meaning it was innocuous, at least compared to today’s cyber threats. Now, we call it a cybercrime.
As a security test, Creeper uninstalled itself from its previous host whenever a new hard drive was infected. Then it displayed the message “I’M THE CREEPER. CATCH ME IF YOU CAN!”. If only things were so simple and innocent nowadays!
With current technological advancements, viruses and other malware are more widespread than ever. It makes these menaces an unstoppable force. Thankfully, we have solutions like Norton 360 Antivirus to help us. What cybercrime encompasses and how you can protect yourself are some of the topics we’ll explore in this article.

A Crash Course on Cybercrime
To understand what an unauthorized party can do against you and your data, it’s sometimes helpful to analyze it from the opposite angle. And, as you’ll soon realize, they can do a lot. So much so that the term “cybercrime” was coined. And within this umbrella term, there are others.
For instance, malware encompasses all kinds of software-related threats, while social engineering deals with how to hack you via cons and scams like pretending to be someone you know to steal information, which is commonly known as “phishing.” Norton 360 deluxe is your best ally to avoid cyberthreats on 2023 like stealing your personal data, phishing and other threats.
Perhaps one of the most famous types of viruses is trojans, a term which, again, is an umbrella. You have exploits, rootkits, droppers, DDoS, and much more. They all work differently, but the goal is the same: infect the computer to steal data.
There’s much more than delivering malware to an unsuspecting target or scamming them via social engineering. Other vulnerabilities cybercriminals take advantage of include weak passwords, connecting to unsafe networks, and being careless with personal data.
Ingenuity abounds in cybercrime. There’s a common attack known as “man-in-the-middle.” In this scheme, someone can redirect you to your desired website by acting as an intermediary. This way, the attacker is privy to all information circulating from and to your device. It can include usernames, passwords, credit card data, and much more.
What’s worse is the scale of some attacks. In our interconnected world, millions of devices can be hacked at the same time, revealing the personal details of many. These details are often shared in hacking forums and the deep web in what is known as “data breaches,” which we’ll discuss later on.
This is just the beginning. Because cybersecurity is akin to an arms race, every new solution to prevent these situations is met with yet another criminal development trying to circumvent it. Thus, it’s imperative to be up-to-date with the best cybersecurity tools at your disposal.

Some Notorious Examples
As of 2023, the worst data breach in history was the Cam4 data breach of March 2020. This is an adult streaming website where 11 billion records were exposed. This included full names, email addresses, and payment logs, but that’s not all.
Because the email content was stored in Gmail, Hotmail, and other popular providers, a lot of media, such as pictures and videos, were also exposed. And, because of the website’s nature, cybercriminals used “sextortion” tactics to demand ransoms. Norton 360 Antivirus is specifically designed to avoid Data breaches and ensure you browse provide your personal data safely
If you think that this only happens to unsuspecting, gullible people, think again. Major organizations and governments with on-site security teams are also under menace. For instance, in July 2023, the parliament of New Zealand was hacked by a Russian group.
That’s not an isolated incident. In the same month, a South Korean institution was the target of a phishing attack, resulting in 175 million wons lost. The Ministry of Justice in Trinidad and Tobago was hit with a DDoS attack, interrupting court operations throughout the country.
As you can see, successful hacking attempts abound and discriminate against no one. In our era, having proper protection is paramount, as is being constantly updated when new threats emerge. Some situations are unavoidable because they are beyond a user’s control, such as a data leak from a website. Others fall under the user’s responsibility, such as keeping your devices safe.

Where Is It Headed?
In our ever-changing online landscape, predicting how cyberattacks will evolve is difficult. Paradigm-breaking technologies such as VR (Virtual Reality) will undoubtedly offer new and creative ways for these nefarious actors to develop innovative ways to break havoc.
Still, the ultimate goal of attacks is the same: allow maximum damage with the least possible consequences for the perpetrator. That means that future viruses, for example, will keep aiming to become as undetectable as possible.
It’s worrying that with the rise of AI, such as ChatGPT, hackers can now develop malware without even knowing how to code. Thus, there may be more viruses, trojans, rootkits, spyware, and others than ever before.
Another important consideration is that, according to the World Economic Forum, 93% of cyber leaders and 86% of business leaders believe there might be a catastrophic cyber event between 2023-2025. Whereas thinking something doesn’t make it automatically true, the fact that top people in the business believe so makes you take it as a done deal.
The rise in remote working also brings in new dangers. Nowadays, organizations must be on the lookout for threats within their employees’ devices. Even if an employee uses a relatively secure company device, it can still be connected to vulnerable networks.
The good news is that competent security companies have world-class tools on board, like Norton anti-virus and other solutions. They take advantage of new technologies such as AI and Machine Learning to develop efficient solutions in record time. It takes some effort from the user’s side, too. Tools must be updated and have a proven track of being reliable.
Latest from Shaun M Jooste
You may also like

Number Of Dc Fast Charging Ports Reaches 55,580 Amidslower Growth
Read more

It seemed like an impossible enemy, but it was actually the smartest anti-piracy system we’ve ever seen in a video game
Read more

Rising Tariffs and Political Fallout: Tesla Faces Unique Challenges in the EV Market
Read more
How to translate text directly from your phone’s keyboard
Read more
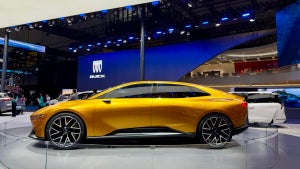
Meet the Buick ELECTRA GS: A Bold Step into the Electric Future
Read more

New Volkswagen ID.UNYX 06 Features Enhanced Tech and Impressive Range
Read more